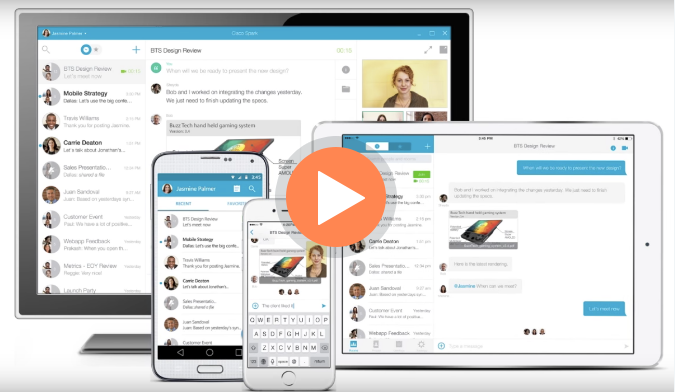
Over the years, technology has allowed us to better collaborate with things such as on-prem phones, smart phones, email, Webex, Skype, and so much more. We use these these products every day and they help us to be more productive in a virtual world where employees and customers are dispersed hundreds to thousands of miles apart.
Cisco Spark: How Are You Building Better Communication?
Feb 27, 2017 / by Bird Rock Blogger posted in IT, IT Solutions, BYOD, collaboration, VOIP, Mobility, Spark, Cisco, Communication
802.11ac: Is It Time to Invest?
Jan 20, 2017 / by Bird Rock Blogger posted in IT, IT Solutions, Wireless, BYOD, IT Services
There is no one simple answer here. At some point, maybe in 5 years, the time to invest will be “NOW!” But when we talk about investment into 802.11ac, we like to take a slow and progressive approach.
802.11ac: What is all the Hype?
Jan 20, 2017 / by Bird Rock Blogger posted in IT, IT Solutions, Wireless, BYOD, IT Services, 802.11ac
The news is out. 802.11ac is worlds faster than 802.11n. Or is it?
BYOD – It can be done safely - Part 3
Nov 06, 2014 / by Joseph Javien posted in Firewall, Security, BYOD
Written By Larry Hoehn
In my previous post, I discussed how wireless technology has a role when providing secure BYOD access. Along those lines, this article explains firewall technology’s role for a secure BYOD initiative.
Today's corporate workforce expects to access their corporate networks from personal mobile devices used both inside and outside the corporate walls. Providing this access to employees and contractors drives productivity gains and fosters innovation. While the benefits can justify the requirement, BYOD introduces elements of risk that legacy technologies have a difficult time addressing.
Old-school firewall port and protocol-based security focus on attacks directed from the outside in. This method assumes that devices inside the network are trusted, since they allow access without consideration for the user’s identity, the device type, or the application in use. This leaves organizations open to attacks from inside the network.
Modern solutions take a new approach – these solutions map user and device information to network security policies, enabling IT to enforce what a user can access with a particular device and authorized application. Firewall policies can also enforce, among other things, bandwidth on a per-user or per-department basis.
How this works:
- Users and devices connect to the network.
- Wired or Wireless architecture shares contextual data (IP address, device type, user role) with the firewall.
- The firewall monitors for policy violations to the network based on who and what is connected to the infrastructure.
- Applications can be controlled based on who and what is connected to the infrastructure, or blocked if there’s no legitimate use.
The big benefit:
Security against known and unknown malware, zero-day exploits, and advanced persistent threats. The firewall automatically implements and enforces protection in near real-time to defend against dynamic attacks.
Stay tuned for my next article, where I’ll discuss a solution with a product use case!
BYOD – It can be done safely - Part 2
Aug 20, 2014 / by Joseph Javien posted in Security, Wireless, BYOD
Written By: Larry Hoehn
In my last post, I discussed combining technologies to provide secure BYOD access. Before we jump into the specifics, let’s pick apart the technology components – starting with the wireless technology.
Modern wireless solutions provide awareness of all traffic across the network to support a variety of users, devices, and applications. Old-school network architectures mandate that parallel networks be constructed to address different needs– for example, one VLAN for employees, a second for full-time contractors, and a third for guests. In other cases, multiple SSIDs were required. Today’s design methods support multiple user categories on a single network.
How It Works
During the network sign-on process, the identity and role of each user or device is learned. Employees and other authorized users may be treated as a single class, or divided according to a series of administrator-defined policies. These policies follow the user throughout the network, and are applied uniformly across wireless, wired, and remote access connections.
Learn This
This entire premise is made possible by using a firewall instance around every user: tightly controlling what the user is permitted to do and providing separation between user classes. To provide the highest level of security, the solution requires knowledge of user identity when making access control decisions. Our wireless and next-generation firewall solutions enable us to deliver this level of security.
The wireless technologies we work with provide us an important point of authentication and policy enforcement. Policy control is tied to user identity rather than port, IP address, or MAC address. This makes it impossible for a user to bypass security controls, except in the case of breached credentials. (Protect your passwords! We will talk about that in a future post.)
A use case for this is a guest user on the guest network that attempts to bypass the guest network by configuring a laptop with the MAC address and IP address of an employee also known as spoofing an address. With the proper policies in place, that malicious guest user will be denied access to the employee network because of his guest privileges regardless of mac address or IP address of the device.
Role Based Policy, Granular Control & API Integration
Taking this a step further, role-based policies can limit maximum and guarantee minimum amounts of bandwidth for a particular user or class of users. This allows IT to provision a specified amount of service to bandwidth-hungry applications. In addition, granular control of users, such as automatic disconnect from the network, role re-assignment, and dynamic updates of firewall policies are available as well.
Behind the scenes, additional functionality is enabled by powerful API integration between various IT solutions from different manufacturers. The APIs can enable captive portal authentication systems, or query external databases to control advanced behavior. This includes integration with solutions that provide services such as virus protection, content inspection and filtering, intrusion detection and prevention, and content transformation.
An example of this could be a posture assessment. A check can be performed to make sure anti-virus scans have been run within the past week and provide different network access depending on the criteria of this test.
We Can Help!
As you can see, there is a lot of flexibility, control and added security that can be delivered with the proper solutions, policy and controls in place when it comes to BYOD. For more information, please contact your local Bird Rock Systems Account Manager or send us a message on our Contact page.
In my next post, I will do a deeper dive on the next-generation firewall part of the equation. Then I’ll wrap the wireless and firewall technologies together. Stay tuned!
Photo credit: John.Karakatsanis / Foter / Creative Commons Attribution-ShareAlike 2.0 Generic (CC BY-SA 2.0)
UT San Diego: Use of Personal Devices at Work Gaining Acceptance More Personal Devices Seen at Work
Nov 25, 2013 / by Joseph Javien posted in In The News, Jim Matteo, Security, BYOD
Growing BYOD trend still raises security concerns
These days, employees are bringing to their workplaces their own personal devices, like smart phones, tablets and laptops.
In the past, a lot of companies weren’t too keen on the idea of allowing workers to use their own equipment. The overriding concern was about security of company data, as well as being uncomfortable with employees storing work information on personal devices.
Now, it appears that such thinking is starting to change. There’s a phenomenon spreading through business across the country that’s known as Bring Your Own Device, or BYOD.
“As companies keep recruiting millennials, BYOD is going to be important in keeping them happy,” said Jim Matteo, CEO of San Diego-based Bird Rock Systems, which provides network security solutions for a wide variety of businesses.
For the full story visit:
http://www.utsandiego.com/news/2013/nov/25/tp-use-of-personal-devices-at-work-gaining/